On April 2023, the Division of Homeland Safety (DHS) Cybersecurity & Infrastructure Safety Company (CISA) launched their Zero Belief Maturity Mannequin Model 2.0 (ZTMM) as “one among many paths that a company can absorb designing and implementing their transition plan to zero belief architectures in accordance with Government Order (EO) 14028 ‘Bettering the Nation’s Cybersecurity’ which requires that companies develop a plan to implement a Zero Belief Structure (ZTA).”
What’s zero belief?
Zero belief just isn’t a product. It’s a mindset, a path towards higher safety that features a set of core capabilities and an strategy that emphasizes the idea of least privileged entry.
A “by no means belief, all the time confirm” strategy means granting least privilege entry primarily based on a dynamic analysis of the trustworthiness of customers and their gadgets and any transaction danger earlier than they’re allowed to connect with community sources.
Step 0 – Perceive the Belongings and Workflows within the Setting
Earlier than implementing an operational strategy with such far-reaching and strategic results, getting the basics proper is necessary. Don’t go to Step 1 with out beginning right here! NIST SP 800-207 emphasizes that an enterprise can’t decide what new processes or methods have to be in place if there isn’t any data of the present state of operations. Actually, NIST emphasizes that earlier than beginning an enterprise’s journey into zero belief, having a “survey of belongings, topics, dataflows, and workflows” stays a necessity. Additional, NIST reminds us that “creating entry insurance policies round acceptable danger to the designated mission or enterprise course of” is essential to any zero belief deployment.
Likewise, the CISA ZTMM emphasizes “alignment with NIST’s steps for transitioning to zero belief” and that “companies ought to assess their present enterprise methods, sources, infrastructure, personnel, and processes earlier than investing in zero belief capabilities.” Moreover, the CISA information makes reference to NIST CSWP 20: “Planning for a Zero Belief Structure: A Planning Information for Federal Directors” which describes the significance of following the deliberate steps of the Danger Administration Framework to assist an enterprise focus on, develop, and implement a ZTA. Suffice it to say, specializing in the basics of figuring out your surroundings and making use of a risk-informed strategy to creating coverage stays important earlier than beginning your journey to zero belief.
How the Logical Elements and Pillars Work Collectively
Insurance policies will be developed and deployed by the Coverage Determination Level (PDP) to allow granular, least privilege entry controls which are enforced in probably the most optimum Coverage Enforcement Level (PEP). Insurance policies are calculated with enter from as many sources and with as a lot context as attainable to tell the coverage engine. A risk-informed understanding of the suitable workflows and information flows is important to creating these insurance policies. All community exercise have to be seen, understood, repeatedly inspected, and logged. Any indications of compromise or variations in habits modifications between customers and gadgets, and sources have to be investigated, validated, and responded to right away to mitigate extra dangers (Determine 1).
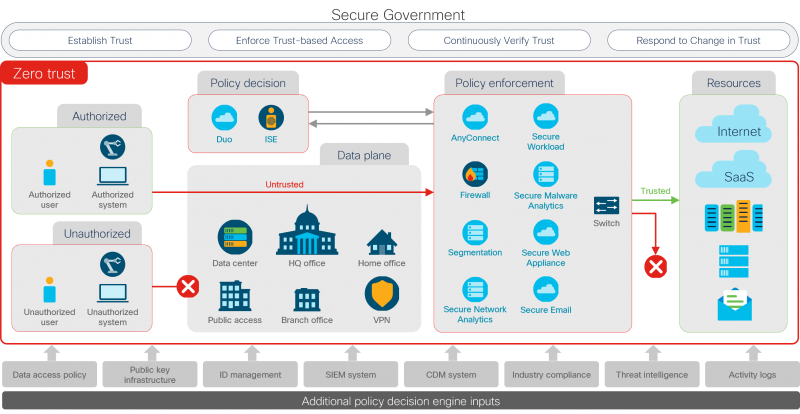
The CISA ZTMM makes use of a maturity mannequin to explain the required capabilities allotted throughout a number of pillars. Underpinning the “core 5 pillars,” the visibility & analytics capabilities help all the capabilities within the pillars of identification, gadgets, networks, functions & workloads, and information. Likewise, automation & orchestration help, economize, and harmonize all zero belief capabilities and operations throughout the pillar. To notice the zero belief logical working mannequin from Determine 1, you will need to be aware that the capabilities should work throughout pillars wholistically—not by themselves in a pillar or “silo.”
Cisco’s open standards-based built-in capabilities allow authorities enterprises to take a 4-step cross-pillar strategy to assist authorities organizations to ship safe mission outcomes with zero belief.

Easy methods to Apply a Zero Belief Operational Mannequin in 4 Steps
A sensible strategy for realizing a zero belief journey will be encapsulated in an operational, four-step, cyclical strategy:
- Set up belief ranges for customers and gadgets, IoT, and/or workloads – visibility and analytics are key to understanding topics, belongings, their state of compliance, and workflows.
- Implement trust-based entry utilizing logical segmentation to manage community entry (making use of macro-segmentation and micro-segmentation) and SD-perimeters to manage utility entry – automation and orchestration work on the pace of the community to implement coverage.
- Repeatedly confirm belief with visibility & analytics – gathering and analyzing telemetry throughout all 5 “core pillars,” monitoring person habits, alerting on potential IOCs, and figuring out vulnerabilities – working with automation and orchestration to quarantine gadgets and isolate potential threats.
- Reply to modifications in belief powered by visibility & analytics, working intently with automation & orchestration to allow prioritized incident response and remediation.
Repeatedly making use of these steps helps drive safety resilience to your group and may also help you to strengthen your safety posture with the facility to grasp danger publicity, spring again from disruption, and restrict the affect of incidents. Cisco options combine together with your present community and the capabilities you have already got. They ship visibility and analytics to know and management what connects to your community. And so they present capabilities from computerized menace updates to machine studying to behavioral modeling that may make it easier to outsmart rising threats. All of it made simpler to handle and extra environment friendly by built-in, automated orchestration by a resilient platform.
Be taught extra
Go deeper into how Cisco may also help you frustrate attackers, not customers, and how Cisco permits zero belief safety.
Try the sources and movies on Safety Resilience for Authorities and discover use circumstances for presidency at Portfolio Explorer for Authorities.
Share:
