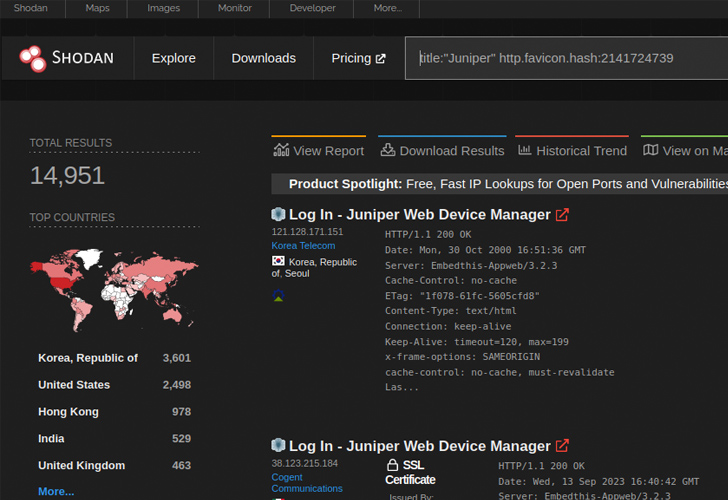
New analysis has discovered that near 12,000 internet-exposed Juniper firewall units are weak to a lately disclosed distant code execution flaw.
VulnCheck, which found a brand new exploit for CVE-2023-36845, stated it might be exploited by an “unauthenticated and distant attacker to execute arbitrary code on Juniper firewalls with out making a file on the system.”
CVE-2023-36845 refers to a medium-severity flaw within the J-Internet part of Junos OS that might be weaponized by a menace actor to manage sure, essential setting variables. It was patched by Juniper Networks final month alongside CVE-2023-36844, CVE-2023-36846, and CVE-2023-36847 in an out-of-cycle replace.

A subsequent proof-of-concept (PoC) exploit devised by watchTowr mixed CVE-2023-36846 and CVE-2023-36845 to add a PHP file containing malicious shellcode and obtain code execution.
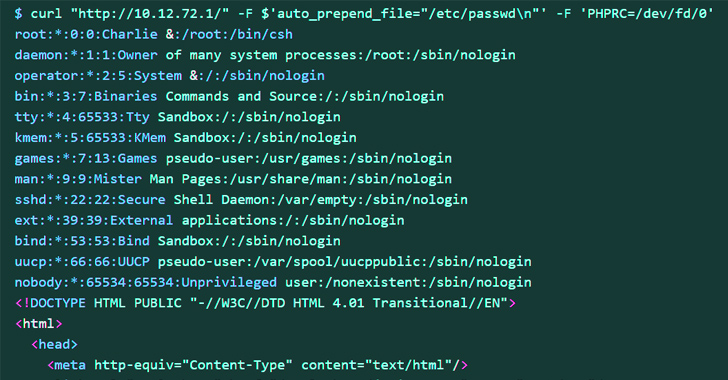
The newest exploit, alternatively, impacts older techniques and might be written utilizing a single cURL command. Particularly, it depends on simply CVE-2023-36845 to understand the identical goal.
This, in flip, is achieved by utilizing the usual enter stream (aka stdin) to set the PHPRC setting variable to “/dev/fd/0” by way of a specifically crafted HTTP request, successfully turning “/dev/fd/0” right into a makeshift file, and leak delicate info.
Arbitrary code execution is then achieved by leveraging PHP’s auto_prepend_file and allow_url_include choices along side the information:// protocol wrapper.
Id is the New Endpoint: Mastering SaaS Safety within the Fashionable Age
Dive deep into the way forward for SaaS safety with Maor Bin, CEO of Adaptive Defend. Uncover why id is the brand new endpoint. Safe your spot now.
“Firewalls are attention-grabbing targets to APT as they assist bridge into the protected community and may function helpful hosts for C2 infrastructure,” Jacob Baines stated. “Anybody who has an unpatched Juniper firewall ought to study it for indicators of compromise.”
Juniper has since disclosed that it isn’t conscious of a profitable exploit in opposition to its clients, however warned that it has detected exploitation makes an attempt within the wild, making it crucial that customers apply the required fixes to mitigate potential threats.